User Management: Difference between revisions
Jump to navigation
Jump to search
| Line 8: | Line 8: | ||
By using the role based user- and permission management for all objects (VM´s, storages, nodes, etc.) granular access can be defined. | By using the role based user- and permission management for all objects (VM´s, storages, nodes, etc.) granular access can be defined. | ||
=Authentication= | =Authentication Realms= | ||
Proxmox VE stores all user attributes in /etc/pve/users.cfg. So there must be an entry for each user in that file. The password is not stored, instead you can use the following methods to verify passwords. | Proxmox VE stores all user attributes in /etc/pve/users.cfg. So there must be an entry for each user in that file. The password is not stored, instead you can use the following methods to verify passwords. | ||
Revision as of 07:56, 23 February 2012
| Note: Article about Proxmox VE 2.0 beta |
draft.
Introduction
Proxmox VE supports multiple authentication sources, e.g. Microsoft Active Directory, LDAP, Linux PAM or the integrated Proxmox VE authentication server.
By using the role based user- and permission management for all objects (VM´s, storages, nodes, etc.) granular access can be defined.
Authentication Realms
Proxmox VE stores all user attributes in /etc/pve/users.cfg. So there must be an entry for each user in that file. The password is not stored, instead you can use the following methods to verify passwords.
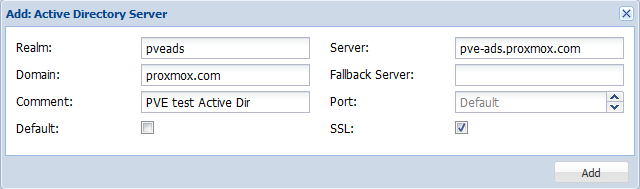
Microsoft Active Directory
LDAP
Linux PAM standard authentication
Proxmox VE authentication server
This is a unix like password store (/etc/pve/priv/shadow.cfg). Password are encrypted using the SHA-256 hash method. Users are allowed to change passwords.