Two-Factor Authentication: Difference between revisions
| Line 64: | Line 64: | ||
nano /etc/pve/user.cfg | nano /etc/pve/user.cfg | ||
user:root@pam:1:0::::OATH Secret: | user:root@pam:1:0::::OATH Secret:Q3Y0UROATHKEYGEN7: | ||
Revision as of 11:12, 21 August 2014
Introduction
Two-factor authentication adds an additional layer of security by introducing a second step to your login to the Proxmox VE web interface. Additionally to the existing username/password, a one-time password (OTP) is used. A new OTP will be required for each new login session. Once generated it will remain valid for 30 min (default value).
Proxmox VE 3.3 (currently beta) offers two different methods:
- Time Based One-Time Passwords (TOTP)
- YubiKey
Time Based One-Time Passwords
Initiative for Open Authentication (OATH) is an industry-wide collaboration to develop an open reference architecture using open standards to promote the adoption of strong authentication. It has close to thirty coordinating and contributing members and is proposing standards for a variety of authentication technologies, with the aim of lowering costs and simplifying their use. For details see the official website
It combines a secret key with the current timestamp using a cryptographic hash function to generate a one-time password. The timestamp typically increases in 30-second intervals, so passwords generated close together in time from the same secret key will be equal.
In a typical two-factor authentication application, user authentication proceeds as follows: a user will enter username and password into a website or other server, generate a one-time password for the server using TOTP running locally on a smartphone or other device, and type that password into the server as well. The server will then also run TOTP to verify the entered one-time password. wikipedia
Configuration
Using a time based one-time password requires just downloading an OATH application onto your smartphone or tablet - e.g. Google Authenticator for Android - No extra hardware and no internet connection.
Two-factor authentication (TFA) can be enabled on any authentication realm. In this howto I describe the steps for the realm "Proxmox VE authentication server". As soon as you enabled OATH for a authentication realm, only users with a configured secret can login. Make sure that you are logged in as root for this configuration changes.
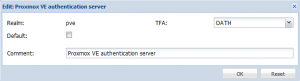
1. Enable TFA (select OATH) on the authentication realm.
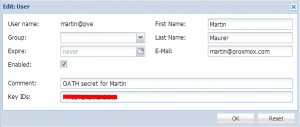
2. Add a unique secret (password) to each user - this secret has also to be added to your OATH app on the smartphone of each user. To generate a secret, you can run the following command on your Proxmox VE host:
oathkeygen
If a user has more secrets, just add all your secrets separated with spaces.
3. Install the OATH app on your smartphone, add a new account and add the secret from above.
In order to test, just use another browser. I used Firefox doing the configuration with root@pam, so I test the TFA login with Chrome.
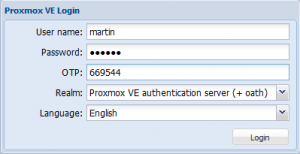
- Select the Authentication Realm
- Enter username and password
- Start the app on your smartphone and add the displayed code into the OTP field. Each code is valid for 30 seconds. In order to get you more time for entering and also a protection against small time differences between your Proxmox VE host and your smartphone, we added a 30 seconds grace period (before and after)
YubiKey
YubiKey creates a one time password stored within a USB drive that acts as a keyboard to your computer. These are physical devices that need to be purchased from Yubico directly, see http://www.yubico.com/
In order to login with YubiKey, you need:
- the YubiKey (USB device)
- internet connection
Configuration
As soon as you got your YubiKey, you can immediately start using it. Two-factor authentication can be enabled on any authentication realm. In this howto I describe the steps for the realm "Proxmox VE authentication server". As soon as you enabled YubiKey for a authentication realm, only users with a YubiKey can login. Make sure that you are logged in as root for this configuration changes.
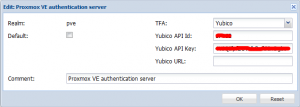
1. Enable TFA (select Yubico) on the authentication realm and add the Yubico API key (you can get the API key from www.yubico.com). A valid API key allows the access and use of the Yubico Servers. This has to be done only once per realm.
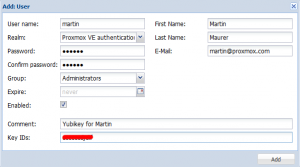
2. Add the Yubikey ID to each user. In order to get the key id from the USB device, just plugin the Yubikey and press the button on the key. The first 12 characters represent the key id (just delete the rest). Repeat this step for all users of this realm. Of course, each user needs a separate key. If a user has more keys, just add all your key ids separated with a space.
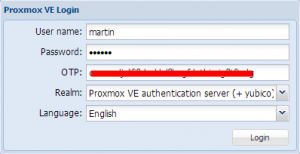
In order to test, just use another browser. I used Firefox doing the configuration with root@pam, so I test the TFA login with Chrome.
- Select the Authentication Realm
- Enter username and password
- Click into the OTA field and press the button on your Yubikey
Troubleshooting
If you've got TFA enabled but have no OATH secret associated to user. eg. Forgot or accidentally logged off. ssh and manually add to the end of line
nano /etc/pve/user.cfg user:root@pam:1:0::::OATH Secret:Q3Y0UROATHKEYGEN7: