User Management: Difference between revisions
(→Pools) |
No edit summary |
||
| Line 22: | Line 22: | ||
This is a unix like password store (/etc/pve/priv/shadow.cfg). Password are encrypted using the SHA-256 hash method. Users are allowed to change passwords. | This is a unix like password store (/etc/pve/priv/shadow.cfg). Password are encrypted using the SHA-256 hash method. Users are allowed to change passwords. | ||
=Users= | =Terms and Definitions= | ||
==Users== | |||
A Proxmox VE user name consists of 2 parts: <userid>@<realm>. The login screen on the GUI shows them a separate items, but it is internally used as single string. | A Proxmox VE user name consists of 2 parts: <userid>@<realm>. The login screen on the GUI shows them a separate items, but it is internally used as single string. | ||
| Line 35: | Line 37: | ||
* comment | * comment | ||
==Superuser== | ===Superuser=== | ||
The traditional unix superuser account is called 'root@pam'. All system mails are forwarded to the email assigned to that account. | The traditional unix superuser account is called 'root@pam'. All system mails are forwarded to the email assigned to that account. | ||
=Groups= | ==Groups== | ||
Each user can be member of several groups. Groups are the preferred way to organize access permissions. You should always grant permission to groups instead of using individual users. That way you will get a much shorter access control list which is easier to handle. | Each user can be member of several groups. Groups are the preferred way to organize access permissions. You should always grant permission to groups instead of using individual users. That way you will get a much shorter access control list which is easier to handle. | ||
=Objects and Paths= | ==Objects and Paths== | ||
Access permissions are assinged to objects, such as a virtual machines (/vms/{vmid}) or a storage (/storage/{storeid}). We use filesystem like paths to address those objects. Those paths forms a natural tree, and permissions can be inherited down that hierachy. | Access permissions are assinged to objects, such as a virtual machines (/vms/{vmid}) or a storage (/storage/{storeid}). We use filesystem like paths to address those objects. Those paths forms a natural tree, and permissions can be inherited down that hierachy. | ||
=Privileges= | ==Privileges== | ||
A privilege is the right to perform a specific action. To simplify management, lists of privileges are grouped into roles, which can then be uses to set permissions. | A privilege is the right to perform a specific action. To simplify management, lists of privileges are grouped into roles, which can then be uses to set permissions. | ||
| Line 60: | Line 62: | ||
* Pool.Allocate: create/remove/modify a pool. | * Pool.Allocate: create/remove/modify a pool. | ||
==Virtual machine related privileges== | ===Virtual machine related privileges=== | ||
* VM.Allocate: create/remove new VM to server inventory | * VM.Allocate: create/remove new VM to server inventory | ||
| Line 77: | Line 79: | ||
* VM.Config.Options: modify any other VM configuration | * VM.Config.Options: modify any other VM configuration | ||
==Storage related privileges== | ===Storage related privileges=== | ||
* Datastore.Allocate: create/remove/modify a data store, delete volumes | * Datastore.Allocate: create/remove/modify a data store, delete volumes | ||
| Line 84: | Line 86: | ||
* Datastore.Audit: view/browse a datastore | * Datastore.Audit: view/browse a datastore | ||
=Roles= | ==Roles== | ||
A role is simply a list of privileges. Proxmox VE comes with a number of predefined roles which satisfies most needs. | A role is simply a list of privileges. Proxmox VE comes with a number of predefined roles which satisfies most needs. | ||
| Line 97: | Line 99: | ||
You can see the whole set of predefined roles on the GUI. | You can see the whole set of predefined roles on the GUI. | ||
=Permissions= | ==Permissions== | ||
Permissions are the way we control access to objects. In technical terms they are simply a triple containing <path,user,role>. This concept is also known as access control lists. Each permission specifies a subject (user or group) and a role (set of privileges) on a specific path. | Permissions are the way we control access to objects. In technical terms they are simply a triple containing <path,user,role>. This concept is also known as access control lists. Each permission specifies a subject (user or group) and a role (set of privileges) on a specific path. | ||
| Line 103: | Line 105: | ||
When a subject requests an action on an object, the framework looks up the roles assigned to that subject (using the object path). The set of roles defines the granted privileges. | When a subject requests an action on an object, the framework looks up the roles assigned to that subject (using the object path). The set of roles defines the granted privileges. | ||
=Pools= | ==Pools== | ||
Pools can be used to group a set of virtual machines and data stores. You can then simply set permissions on pools (/pool/{poolid}), which are inherited to all pool members. This is a great way simplify access control. | Pools can be used to group a set of virtual machines and data stores. You can then simply set permissions on pools (/pool/{poolid}), which are inherited to all pool members. This is a great way simplify access control. | ||
Revision as of 09:28, 23 February 2012
| Note: Article about Proxmox VE 2.0 beta |
draft.
Introduction
Proxmox VE supports multiple authentication sources, e.g. Microsoft Active Directory, LDAP, Linux PAM or the integrated Proxmox VE authentication server.
By using the role based user- and permission management for all objects (VM´s, storages, nodes, etc.) granular access can be defined.
Authentication Realms
Proxmox VE stores all user attributes in /etc/pve/users.cfg. So there must be an entry for each user in that file. The password is not stored, instead you can use configure serveral realms to verify passwords.
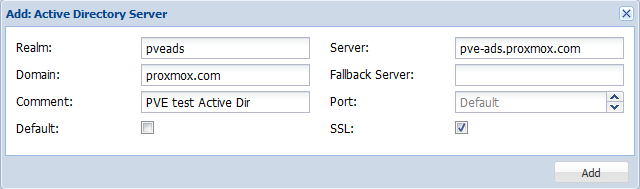
Microsoft Active Directory
LDAP
Linux PAM standard authentication
Proxmox VE authentication server
This is a unix like password store (/etc/pve/priv/shadow.cfg). Password are encrypted using the SHA-256 hash method. Users are allowed to change passwords.
Terms and Definitions
Users
A Proxmox VE user name consists of 2 parts: <userid>@<realm>. The login screen on the GUI shows them a separate items, but it is internally used as single string.
We store the following attribute for users (/etc/pve/user.cfg):
- first name
- last name
- email address
- expiration date
- flag to enable/disable account
- comment
Superuser
The traditional unix superuser account is called 'root@pam'. All system mails are forwarded to the email assigned to that account.
Groups
Each user can be member of several groups. Groups are the preferred way to organize access permissions. You should always grant permission to groups instead of using individual users. That way you will get a much shorter access control list which is easier to handle.
Objects and Paths
Access permissions are assinged to objects, such as a virtual machines (/vms/{vmid}) or a storage (/storage/{storeid}). We use filesystem like paths to address those objects. Those paths forms a natural tree, and permissions can be inherited down that hierachy.
Privileges
A privilege is the right to perform a specific action. To simplify management, lists of privileges are grouped into roles, which can then be uses to set permissions.
We currently use the following privileges:
- Permissions.Modify: modify access permissions
- Sys.PowerMgmt: Node power management (start, stop, reset, shutdown, ...)
- Sys.Console: console access to Node
- Sys.Syslog: view Syslog
- Sys.Audit: view node status/config
- Pool.Allocate: create/remove/modify a pool.
- VM.Allocate: create/remove new VM to server inventory
- VM.Migrate: migrate VM to alternate server on cluster
- VM.PowerMgmt: power management (start, stop, reset, shutdown, ...)
- VM.Console: console access to VM
- VM.Monitor: access to VM monitor (kvm)
- VM.Backup: backup/restore VMs
- VM.Audit: view VM config
- VM.Config.Disk: add/modify/delete Disks
- VM.Config.CDROM: eject/change CDROM
- VM.Config.CPU: modify CPU settings
- VM.Config.Memory: modify Memory settings
- VM.Config.Network: add/modify/delete Network devices
- VM.Config.HWType: modify emulated HW type
- VM.Config.Options: modify any other VM configuration
- Datastore.Allocate: create/remove/modify a data store, delete volumes
- Datastore.AllocateSpace: allocate space on a datastore
- Datastore.AllocateTemplate: allocate/upload templates and iso images
- Datastore.Audit: view/browse a datastore
Roles
A role is simply a list of privileges. Proxmox VE comes with a number of predefined roles which satisfies most needs.
- Administrator: has all privileges
- NoAccess: has no privileges (used to forbid access)
- PVEAdmin: can do most things, but miss rights to modify system settings (Sys.PowerMgmt, Sys.Modify, Realm.Allocate).
- PVEAuditor: read only access
You can see the whole set of predefined roles on the GUI.
Permissions
Permissions are the way we control access to objects. In technical terms they are simply a triple containing <path,user,role>. This concept is also known as access control lists. Each permission specifies a subject (user or group) and a role (set of privileges) on a specific path.
When a subject requests an action on an object, the framework looks up the roles assigned to that subject (using the object path). The set of roles defines the granted privileges.
Pools
Pools can be used to group a set of virtual machines and data stores. You can then simply set permissions on pools (/pool/{poolid}), which are inherited to all pool members. This is a great way simplify access control.