User Management
| Note: Article about Proxmox VE 2.0 beta |
draft.
Introduction
Proxmox VE supports multiple authentication sources, e.g. Microsoft Active Directory, LDAP, Linux PAM or the integrated Proxmox VE authentication server.
By using the role based user- and permission management for all objects (VM´s, storages, nodes, etc.) granular access can be defined.
Authentication Realms
Proxmox VE stores all user attributes in /etc/pve/users.cfg. So there must be an entry for each user in that file. The password is not stored, instead you can use configure serveral realms to verify passwords.
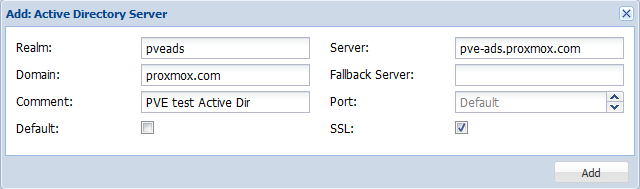
Microsoft Active Directory
LDAP
Linux PAM standard authentication
Proxmox VE authentication server
This is a unix like password store (/etc/pve/priv/shadow.cfg). Password are encrypted using the SHA-256 hash method. Users are allowed to change passwords.
Users
A Proxmox VE user name consists of 2 parts: <userid>@<realm>. The login screen on the GUI shows them a separate items, but it is internally used as single string.
We store the following attribute for users (/etc/pve/user.cfg):
- first name
- last name
- email address
- expiration date
- flag to enable/disable account
- comment
Superuser
The traditional unix superuser account is called 'root@pam'. All system mails are forwarded to the email assigned to that account.