NAME
pvecm - Proxmox VE Cluster Manager
SYNOPSIS
pvecm <COMMAND> [ARGS] [OPTIONS]
pvecm add <hostname> [OPTIONS]
Adds the current node to an existing cluster.
- <hostname>: <string>
-
Hostname (or IP) of an existing cluster member.
- --fingerprint ([A-Fa-f0-9]{2}:){31}[A-Fa-f0-9]{2}
-
Certificate SHA 256 fingerprint.
- --force <boolean>
-
Do not throw error if node already exists.
- --link[n] [address=]<IP> [,priority=<integer>]
-
Address and priority information of a single corosync link. (up to 8 links supported; link0..link7)
- --nodeid <integer> (1 - N)
-
Node id for this node.
- --use_ssh <boolean>
-
Always use SSH to join, even if peer may do it over API.
- --votes <integer> (0 - N)
-
Number of votes for this node
pvecm addnode <node> [OPTIONS]
Adds a node to the cluster configuration. This call is for internal use.
- <node>: <string>
-
The cluster node name.
- --apiversion <integer>
-
The JOIN_API_VERSION of the new node.
- --force <boolean>
-
Do not throw error if node already exists.
- --link[n] [address=]<IP> [,priority=<integer>]
-
Address and priority information of a single corosync link. (up to 8 links supported; link0..link7)
- --new_node_ip <string>
-
IP Address of node to add. Used as fallback if no links are given.
- --nodeid <integer> (1 - N)
-
Node id for this node.
- --votes <integer> (0 - N)
-
Number of votes for this node
pvecm apiver
Return the version of the cluster join API available on this node.
pvecm create <clustername> [OPTIONS]
Generate new cluster configuration. If no links given, default to local IP address as link0.
- <clustername>: <string>
-
The name of the cluster.
- --link[n] [address=]<IP> [,priority=<integer>]
-
Address and priority information of a single corosync link. (up to 8 links supported; link0..link7)
- --nodeid <integer> (1 - N)
-
Node id for this node.
- --votes <integer> (1 - N)
-
Number of votes for this node.
pvecm delnode <node>
Removes a node from the cluster configuration.
- <node>: <string>
-
The cluster node name.
pvecm expected <expected>
Tells corosync a new value of expected votes.
- <expected>: <integer> (1 - N)
-
Expected votes
pvecm help [OPTIONS]
Get help about specified command.
- --extra-args <array>
-
Shows help for a specific command
- --verbose <boolean>
-
Verbose output format.
pvecm keygen <filename>
Generate new cryptographic key for corosync.
- <filename>: <string>
-
Output file name
pvecm mtunnel [<extra-args>] [OPTIONS]
Used by VM/CT migration - do not use manually.
- <extra-args>: <array>
-
Extra arguments as array
- --get_migration_ip <boolean> (default = 0)
-
return the migration IP, if configured
- --migration_network <string>
-
the migration network used to detect the local migration IP
- --run-command <boolean>
-
Run a command with a tcp socket as standard input. The IP address and port are printed via this command’s stdandard output first, each on a separate line.
pvecm nodes
Displays the local view of the cluster nodes.
pvecm qdevice remove
Remove a configured QDevice
pvecm qdevice setup <address> [OPTIONS]
Setup the use of a QDevice
- <address>: <string>
-
Specifies the network address of an external corosync QDevice
- --force <boolean>
-
Do not throw error on possible dangerous operations.
- --network <string>
-
The network which should be used to connect to the external qdevice
pvecm status
Displays the local view of the cluster status.
pvecm updatecerts [OPTIONS]
Update node certificates (and generate all needed files/directories).
- --force <boolean>
-
Force generation of new SSL certificate.
- --silent <boolean>
-
Ignore errors (i.e. when cluster has no quorum).
DESCRIPTION
The Proxmox VE cluster manager pvecm is a tool to create a group of physical servers. Such a group is called a cluster. We use the Corosync Cluster Engine for reliable group communication. There’s no explicit limit for the number of nodes in a cluster. In practice, the actual possible node count may be limited by the host and network performance. Currently (2021), there are reports of clusters (using high-end enterprise hardware) with over 50 nodes in production.
pvecm can be used to create a new cluster, join nodes to a cluster, leave the cluster, get status information and do various other cluster-related tasks. The Proxmox Cluster File System (“pmxcfs”) is used to transparently distribute the cluster configuration to all cluster nodes.
Grouping nodes into a cluster has the following advantages:
-
Centralized, web based management
-
Multi-master clusters: each node can do all management tasks
-
pmxcfs: database-driven file system for storing configuration files, replicated in real-time on all nodes using corosync.
-
Easy migration of virtual machines and containers between physical hosts
-
Fast deployment
-
Cluster-wide services like firewall and HA
Requirements
-
All nodes must be able to connect to each other via UDP ports 5404 and 5405 for corosync to work.
-
Date and time have to be synchronized.
-
SSH tunnel on TCP port 22 between nodes is used.
-
If you are interested in High Availability, you need to have at least three nodes for reliable quorum. All nodes should have the same version.
-
We recommend a dedicated NIC for the cluster traffic, especially if you use shared storage.
-
Root password of a cluster node is required for adding nodes.
|
|
It is not possible to mix Proxmox VE 3.x and earlier with Proxmox VE 4.X cluster nodes. |
|
|
While it’s possible to mix Proxmox VE 4.4 and Proxmox VE 5.0 nodes, doing so is not supported as production configuration and should only used temporarily during upgrading the whole cluster from one to another major version. |
|
|
Running a cluster of Proxmox VE 6.x with earlier versions is not possible. The cluster protocol (corosync) between Proxmox VE 6.x and earlier versions changed fundamentally. The corosync 3 packages for Proxmox VE 5.4 are only intended for the upgrade procedure to Proxmox VE 6.0. |
Preparing Nodes
First, install Proxmox VE on all nodes. Make sure that each node is installed with the final hostname and IP configuration. Changing the hostname and IP is not possible after cluster creation.
While it’s common to reference all nodenames and their IPs in /etc/hosts (or make their names resolvable through other means), this is not necessary for a cluster to work. It may be useful however, as you can then connect from one node to the other with SSH via the easier to remember node name (see also Link Address Types). Note that we always recommend to reference nodes by their IP addresses in the cluster configuration.
Create a Cluster
You can either create a cluster on the console (login via ssh), or through the API using the Proxmox VE Webinterface (Datacenter → Cluster).
|
|
Use a unique name for your cluster. This name cannot be changed later. The cluster name follows the same rules as node names. |
Create via Web GUI
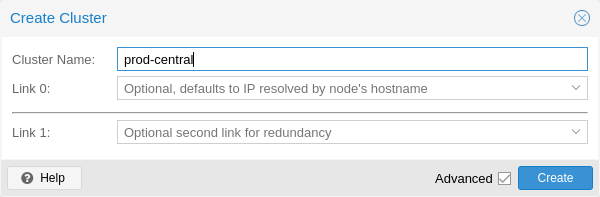
Under Datacenter → Cluster, click on Create Cluster. Enter the cluster name and select a network connection from the dropdown to serve as the main cluster network (Link 0). It defaults to the IP resolved via the node’s hostname.
To add a second link as fallback, you can select the Advanced checkbox and choose an additional network interface (Link 1, see also Corosync Redundancy).
|
|
Ensure the network selected for the cluster communication is not used for any high traffic loads like those of (network) storages or live-migration. While the cluster network itself produces small amounts of data, it is very sensitive to latency. Check out full cluster network requirements. |
Create via Command Line
Login via ssh to the first Proxmox VE node and run the following command:
hp1# pvecm create CLUSTERNAME
To check the state of the new cluster use:
hp1# pvecm status
Multiple Clusters In Same Network
It is possible to create multiple clusters in the same physical or logical network. Each such cluster must have a unique name to avoid possible clashes in the cluster communication stack. This also helps avoid human confusion by making clusters clearly distinguishable.
While the bandwidth requirement of a corosync cluster is relatively low, the latency of packages and the package per second (PPS) rate is the limiting factor. Different clusters in the same network can compete with each other for these resources, so it may still make sense to use separate physical network infrastructure for bigger clusters.
Adding Nodes to the Cluster
|
|
A node that is about to be added to the cluster cannot hold any guests. All existing configuration in /etc/pve is overwritten when joining a cluster, since guest IDs could be conflicting. As a workaround create a backup of the guest (vzdump) and restore it as a different ID after the node has been added to the cluster. |
Join Node to Cluster via GUI
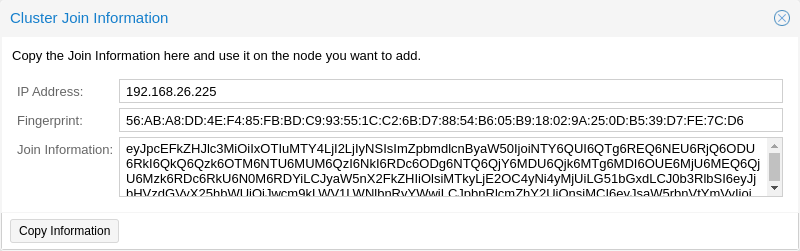
Login to the web interface on an existing cluster node. Under Datacenter → Cluster, click the button Join Information at the top. Then, click on the button Copy Information. Alternatively, copy the string from the Information field manually.
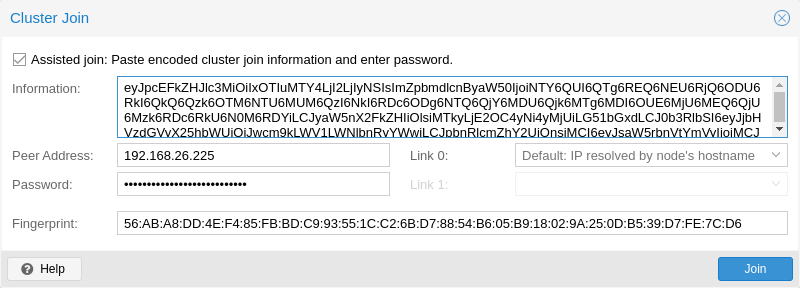
Next, login to the web interface on the node you want to add. Under Datacenter → Cluster, click on Join Cluster. Fill in the Information field with the Join Information text you copied earlier. Most settings required for joining the cluster will be filled out automatically. For security reasons, the cluster password has to be entered manually.
|
|
To enter all required data manually, you can disable the Assisted Join checkbox. |
After clicking the Join button, the cluster join process will start immediately. After the node joined the cluster its current node certificate will be replaced by one signed from the cluster certificate authority (CA), that means the current session will stop to work after a few seconds. You might then need to force-reload the webinterface and re-login with the cluster credentials.
Now your node should be visible under Datacenter → Cluster.
Join Node to Cluster via Command Line
Login via ssh to the node you want to join into an existing cluster.
hp2# pvecm add IP-ADDRESS-CLUSTER
For IP-ADDRESS-CLUSTER use the IP or hostname of an existing cluster node. An IP address is recommended (see Link Address Types).
To check the state of the cluster use:
# pvecm status
hp2# pvecm status
Quorum information
~~~~~~~~~~~~~~~~~~
Date: Mon Apr 20 12:30:13 2015
Quorum provider: corosync_votequorum
Nodes: 4
Node ID: 0x00000001
Ring ID: 1/8
Quorate: Yes
Votequorum information
~~~~~~~~~~~~~~~~~~~~~~
Expected votes: 4
Highest expected: 4
Total votes: 4
Quorum: 3
Flags: Quorate
Membership information
~~~~~~~~~~~~~~~~~~~~~~
Nodeid Votes Name
0x00000001 1 192.168.15.91
0x00000002 1 192.168.15.92 (local)
0x00000003 1 192.168.15.93
0x00000004 1 192.168.15.94
If you only want the list of all nodes use:
# pvecm nodes
hp2# pvecm nodes
Membership information
~~~~~~~~~~~~~~~~~~~~~~
Nodeid Votes Name
1 1 hp1
2 1 hp2 (local)
3 1 hp3
4 1 hp4
Adding Nodes With Separated Cluster Network
When adding a node to a cluster with a separated cluster network you need to use the link0 parameter to set the nodes address on that network:
pvecm add IP-ADDRESS-CLUSTER -link0 LOCAL-IP-ADDRESS-LINK0
If you want to use the built-in redundancy of the kronosnet transport layer, also use the link1 parameter.
Using the GUI, you can select the correct interface from the corresponding Link 0 and Link 1 fields in the Cluster Join dialog.
Remove a Cluster Node
|
|
Read carefully the procedure before proceeding, as it could not be what you want or need. |
Move all virtual machines from the node. Make sure you have no local data or backups you want to keep, or save them accordingly. In the following example we will remove the node hp4 from the cluster.
Log in to a different cluster node (not hp4), and issue a pvecm nodes command to identify the node ID to remove:
hp1# pvecm nodes
Membership information
~~~~~~~~~~~~~~~~~~~~~~
Nodeid Votes Name
1 1 hp1 (local)
2 1 hp2
3 1 hp3
4 1 hp4
At this point you must power off hp4 and make sure that it will not power on again (in the network) as it is.
|
|
As said above, it is critical to power off the node before removal, and make sure that it will never power on again (in the existing cluster network) as it is. If you power on the node as it is, your cluster will be screwed up and it could be difficult to restore a clean cluster state. |
After powering off the node hp4, we can safely remove it from the cluster.
hp1# pvecm delnode hp4 Killing node 4
Use pvecm nodes or pvecm status to check the node list again. It should look something like:
hp1# pvecm status
Quorum information
~~~~~~~~~~~~~~~~~~
Date: Mon Apr 20 12:44:28 2015
Quorum provider: corosync_votequorum
Nodes: 3
Node ID: 0x00000001
Ring ID: 1/8
Quorate: Yes
Votequorum information
~~~~~~~~~~~~~~~~~~~~~~
Expected votes: 3
Highest expected: 3
Total votes: 3
Quorum: 2
Flags: Quorate
Membership information
~~~~~~~~~~~~~~~~~~~~~~
Nodeid Votes Name
0x00000001 1 192.168.15.90 (local)
0x00000002 1 192.168.15.91
0x00000003 1 192.168.15.92
If, for whatever reason, you want this server to join the same cluster again, you have to
-
reinstall Proxmox VE on it from scratch
-
then join it, as explained in the previous section.
|
|
After removal of the node, its SSH fingerprint will still reside in the known_hosts of the other nodes. If you receive an SSH error after rejoining a node with the same IP or hostname, run pvecm updatecerts once on the re-added node to update its fingerprint cluster wide. |
Separate A Node Without Reinstalling
|
|
This is not the recommended method, proceed with caution. Use the above mentioned method if you’re unsure. |
You can also separate a node from a cluster without reinstalling it from scratch. But after removing the node from the cluster it will still have access to the shared storages! This must be resolved before you start removing the node from the cluster. A Proxmox VE cluster cannot share the exact same storage with another cluster, as storage locking doesn’t work over the cluster boundary. Further, it may also lead to VMID conflicts.
Its suggested that you create a new storage where only the node which you want to separate has access. This can be a new export on your NFS or a new Ceph pool, to name a few examples. Its just important that the exact same storage does not gets accessed by multiple clusters. After setting this storage up move all data from the node and its VMs to it. Then you are ready to separate the node from the cluster.
|
|
Ensure all shared resources are cleanly separated! Otherwise you will run into conflicts and problems. |
First, stop the corosync and the pve-cluster services on the node:
systemctl stop pve-cluster systemctl stop corosync
Start the cluster filesystem again in local mode:
pmxcfs -l
Delete the corosync configuration files:
rm /etc/pve/corosync.conf rm -r /etc/corosync/*
You can now start the filesystem again as normal service:
killall pmxcfs systemctl start pve-cluster
The node is now separated from the cluster. You can deleted it from a remaining node of the cluster with:
pvecm delnode oldnode
If the command failed, because the remaining node in the cluster lost quorum when the now separate node exited, you may set the expected votes to 1 as a workaround:
pvecm expected 1And then repeat the pvecm delnode command.
Now switch back to the separated node, here delete all remaining files left from the old cluster. This ensures that the node can be added to another cluster again without problems.
rm /var/lib/corosync/*As the configuration files from the other nodes are still in the cluster filesystem you may want to clean those up too. Remove simply the whole directory recursive from /etc/pve/nodes/NODENAME, but check three times that you used the correct one before deleting it.
|
|
The nodes SSH keys are still in the authorized_key file, this means the nodes can still connect to each other with public key authentication. This should be fixed by removing the respective keys from the /etc/pve/priv/authorized_keys file. |
Quorum
Proxmox VE use a quorum-based technique to provide a consistent state among all cluster nodes.
A quorum is the minimum number of votes that a distributed transaction has to obtain in order to be allowed to perform an operation in a distributed system.
— from Wikipedia
In case of network partitioning, state changes requires that a majority of nodes are online. The cluster switches to read-only mode if it loses quorum.
|
|
Proxmox VE assigns a single vote to each node by default. |
Cluster Network
The cluster network is the core of a cluster. All messages sent over it have to be delivered reliably to all nodes in their respective order. In Proxmox VE this part is done by corosync, an implementation of a high performance, low overhead high availability development toolkit. It serves our decentralized configuration file system (pmxcfs).
Network Requirements
This needs a reliable network with latencies under 2 milliseconds (LAN performance) to work properly. The network should not be used heavily by other members, ideally corosync runs on its own network. Do not use a shared network for corosync and storage (except as a potential low-priority fallback in a redundant configuration).
Before setting up a cluster, it is good practice to check if the network is fit for that purpose. To make sure the nodes can connect to each other on the cluster network, you can test the connectivity between them with the ping tool.
If the Proxmox VE firewall is enabled, ACCEPT rules for corosync will automatically be generated - no manual action is required.
|
|
Corosync used Multicast before version 3.0 (introduced in Proxmox VE 6.0). Modern versions rely on Kronosnet for cluster communication, which, for now, only supports regular UDP unicast. |
|
|
You can still enable Multicast or legacy unicast by setting your transport to udp or udpu in your corosync.conf, but keep in mind that this will disable all cryptography and redundancy support. This is therefore not recommended. |
Separate Cluster Network
When creating a cluster without any parameters the corosync cluster network is generally shared with the Web UI and the VMs and their traffic. Depending on your setup, even storage traffic may get sent over the same network. Its recommended to change that, as corosync is a time critical real time application.
Setting Up A New Network
First, you have to set up a new network interface. It should be on a physically separate network. Ensure that your network fulfills the cluster network requirements.
Separate On Cluster Creation
This is possible via the linkX parameters of the pvecm create command used for creating a new cluster.
If you have set up an additional NIC with a static address on 10.10.10.1/25, and want to send and receive all cluster communication over this interface, you would execute:
pvecm create test --link0 10.10.10.1
To check if everything is working properly execute:
systemctl status corosync
Afterwards, proceed as described above to add nodes with a separated cluster network.
Separate After Cluster Creation
You can do this if you have already created a cluster and want to switch its communication to another network, without rebuilding the whole cluster. This change may lead to short durations of quorum loss in the cluster, as nodes have to restart corosync and come up one after the other on the new network.
Check how to edit the corosync.conf file first. Then, open it and you should see a file similar to:
logging {
debug: off
to_syslog: yes
}
nodelist {
node {
name: due
nodeid: 2
quorum_votes: 1
ring0_addr: due
}
node {
name: tre
nodeid: 3
quorum_votes: 1
ring0_addr: tre
}
node {
name: uno
nodeid: 1
quorum_votes: 1
ring0_addr: uno
}
}
quorum {
provider: corosync_votequorum
}
totem {
cluster_name: testcluster
config_version: 3
ip_version: ipv4-6
secauth: on
version: 2
interface {
linknumber: 0
}
}
|
|
ringX_addr actually specifies a corosync link address, the name "ring" is a remnant of older corosync versions that is kept for backwards compatibility. |
The first thing you want to do is add the name properties in the node entries if you do not see them already. Those must match the node name.
Then replace all addresses from the ring0_addr properties of all nodes with the new addresses. You may use plain IP addresses or hostnames here. If you use hostnames ensure that they are resolvable from all nodes. (see also Link Address Types)
In this example, we want to switch the cluster communication to the 10.10.10.1/25 network. So we replace all ring0_addr respectively.
|
|
The exact same procedure can be used to change other ringX_addr values as well, although we recommend to not change multiple addresses at once, to make it easier to recover if something goes wrong. |
After we increase the config_version property, the new configuration file should look like:
logging {
debug: off
to_syslog: yes
}
nodelist {
node {
name: due
nodeid: 2
quorum_votes: 1
ring0_addr: 10.10.10.2
}
node {
name: tre
nodeid: 3
quorum_votes: 1
ring0_addr: 10.10.10.3
}
node {
name: uno
nodeid: 1
quorum_votes: 1
ring0_addr: 10.10.10.1
}
}
quorum {
provider: corosync_votequorum
}
totem {
cluster_name: testcluster
config_version: 4
ip_version: ipv4-6
secauth: on
version: 2
interface {
linknumber: 0
}
}
Then, after a final check if all changed information is correct, we save it and once again follow the edit corosync.conf file section to bring it into effect.
The changes will be applied live, so restarting corosync is not strictly necessary. If you changed other settings as well, or notice corosync complaining, you can optionally trigger a restart.
On a single node execute:
systemctl restart corosync
Now check if everything is fine:
systemctl status corosync
If corosync runs again correct restart corosync also on all other nodes. They will then join the cluster membership one by one on the new network.
Corosync addresses
A corosync link address (for backwards compatibility denoted by ringX_addr in corosync.conf) can be specified in two ways:
-
IPv4/v6 addresses will be used directly. They are recommended, since they are static and usually not changed carelessly.
-
Hostnames will be resolved using getaddrinfo, which means that per default, IPv6 addresses will be used first, if available (see also man gai.conf). Keep this in mind, especially when upgrading an existing cluster to IPv6.
|
|
Hostnames should be used with care, since the address they resolve to can be changed without touching corosync or the node it runs on - which may lead to a situation where an address is changed without thinking about implications for corosync. |
A separate, static hostname specifically for corosync is recommended, if hostnames are preferred. Also, make sure that every node in the cluster can resolve all hostnames correctly.
Since Proxmox VE 5.1, while supported, hostnames will be resolved at the time of entry. Only the resolved IP is then saved to the configuration.
Nodes that joined the cluster on earlier versions likely still use their unresolved hostname in corosync.conf. It might be a good idea to replace them with IPs or a separate hostname, as mentioned above.
Corosync Redundancy
Corosync supports redundant networking via its integrated kronosnet layer by default (it is not supported on the legacy udp/udpu transports). It can be enabled by specifying more than one link address, either via the --linkX parameters of pvecm, in the GUI as Link 1 (while creating a cluster or adding a new node) or by specifying more than one ringX_addr in corosync.conf.
|
|
To provide useful failover, every link should be on its own physical network connection. |
Links are used according to a priority setting. You can configure this priority by setting knet_link_priority in the corresponding interface section in corosync.conf, or, preferably, using the priority parameter when creating your cluster with pvecm:
# pvecm create CLUSTERNAME --link0 10.10.10.1,priority=15 --link1 10.20.20.1,priority=20
This would cause link1 to be used first, since it has the higher priority.
If no priorities are configured manually (or two links have the same priority), links will be used in order of their number, with the lower number having higher priority.
Even if all links are working, only the one with the highest priority will see corosync traffic. Link priorities cannot be mixed, i.e. links with different priorities will not be able to communicate with each other.
Since lower priority links will not see traffic unless all higher priorities have failed, it becomes a useful strategy to specify even networks used for other tasks (VMs, storage, etc…) as low-priority links. If worst comes to worst, a higher-latency or more congested connection might be better than no connection at all.
Adding Redundant Links To An Existing Cluster
To add a new link to a running configuration, first check how to edit the corosync.conf file.
Then, add a new ringX_addr to every node in the nodelist section. Make sure that your X is the same for every node you add it to, and that it is unique for each node.
Lastly, add a new interface, as shown below, to your totem section, replacing X with your link number chosen above.
Assuming you added a link with number 1, the new configuration file could look like this:
logging {
debug: off
to_syslog: yes
}
nodelist {
node {
name: due
nodeid: 2
quorum_votes: 1
ring0_addr: 10.10.10.2
ring1_addr: 10.20.20.2
}
node {
name: tre
nodeid: 3
quorum_votes: 1
ring0_addr: 10.10.10.3
ring1_addr: 10.20.20.3
}
node {
name: uno
nodeid: 1
quorum_votes: 1
ring0_addr: 10.10.10.1
ring1_addr: 10.20.20.1
}
}
quorum {
provider: corosync_votequorum
}
totem {
cluster_name: testcluster
config_version: 4
ip_version: ipv4-6
secauth: on
version: 2
interface {
linknumber: 0
}
interface {
linknumber: 1
}
}
The new link will be enabled as soon as you follow the last steps to edit the corosync.conf file. A restart should not be necessary. You can check that corosync loaded the new link using:
journalctl -b -u corosync
It might be a good idea to test the new link by temporarily disconnecting the old link on one node and making sure that its status remains online while disconnected:
pvecm status
If you see a healthy cluster state, it means that your new link is being used.
Role of SSH in Proxmox VE Clusters
Proxmox VE utilizes SSH tunnels for various features.
-
Proxying console/shell sessions (node and guests)
When using the shell for node B while being connected to node A, connects to a terminal proxy on node A, which is in turn connected to the login shell on node B via a non-interactive SSH tunnel.
-
VM and CT memory and local-storage migration in secure mode.
During the migration one or more SSH tunnel(s) are established between the source and target nodes, in order to exchange migration information and transfer memory and disk contents.
-
Storage replication
|
|
Pitfalls due to automatic execution of .bashrc and siblings
In case you have a custom .bashrc, or similar files that get executed on login by the configured shell, ssh will automatically run it once the session is established successfully. This can cause some unexpected behavior, as those commands may be executed with root permissions on any above described operation. That can cause possible problematic side-effects! In order to avoid such complications, it’s recommended to add a check in /root/.bashrc to make sure the session is interactive, and only then run .bashrc commands. You can add this snippet at the beginning of your .bashrc file: # Early exit if not running interactively to avoid side-effects!
case $- in
*i*) ;;
*) return;;
esac
|
Corosync External Vote Support
This section describes a way to deploy an external voter in a Proxmox VE cluster. When configured, the cluster can sustain more node failures without violating safety properties of the cluster communication.
For this to work there are two services involved:
-
a so called qdevice daemon which runs on each Proxmox VE node
-
an external vote daemon which runs on an independent server.
As a result you can achieve higher availability even in smaller setups (for example 2+1 nodes).
QDevice Technical Overview
The Corosync Quorum Device (QDevice) is a daemon which runs on each cluster node. It provides a configured number of votes to the clusters quorum subsystem based on an external running third-party arbitrator’s decision. Its primary use is to allow a cluster to sustain more node failures than standard quorum rules allow. This can be done safely as the external device can see all nodes and thus choose only one set of nodes to give its vote. This will only be done if said set of nodes can have quorum (again) when receiving the third-party vote.
Currently only QDevice Net is supported as a third-party arbitrator. It is a daemon which provides a vote to a cluster partition if it can reach the partition members over the network. It will give only votes to one partition of a cluster at any time. It’s designed to support multiple clusters and is almost configuration and state free. New clusters are handled dynamically and no configuration file is needed on the host running a QDevice.
The external host has the only requirement that it needs network access to the cluster and a corosync-qnetd package available. We provide such a package for Debian based hosts, other Linux distributions should also have a package available through their respective package manager.
|
|
In contrast to corosync itself, a QDevice connects to the cluster over TCP/IP. The daemon may even run outside of the clusters LAN and can have longer latencies than 2 ms. |
Supported Setups
We support QDevices for clusters with an even number of nodes and recommend it for 2 node clusters, if they should provide higher availability. For clusters with an odd node count we discourage the use of QDevices currently. The reason for this, is the difference of the votes the QDevice provides for each cluster type. Even numbered clusters get single additional vote, with this we can only increase availability, i.e. if the QDevice itself fails we are in the same situation as with no QDevice at all.
Now, with an odd numbered cluster size the QDevice provides (N-1) votes — where N corresponds to the cluster node count. This difference makes sense, if we had only one additional vote the cluster can get into a split brain situation. This algorithm would allow that all nodes but one (and naturally the QDevice itself) could fail. There are two drawbacks with this:
-
If the QNet daemon itself fails, no other node may fail or the cluster immediately loses quorum. For example, in a cluster with 15 nodes 7 could fail before the cluster becomes inquorate. But, if a QDevice is configured here and said QDevice fails itself no single node of the 15 may fail. The QDevice acts almost as a single point of failure in this case.
-
The fact that all but one node plus QDevice may fail sound promising at first, but this may result in a mass recovery of HA services that would overload the single node left. Also ceph server will stop to provide services after only ((N-1)/2) nodes are online.
If you understand the drawbacks and implications you can decide yourself if you should use this technology in an odd numbered cluster setup.
QDevice-Net Setup
We recommend to run any daemon which provides votes to corosync-qdevice as an unprivileged user. Proxmox VE and Debian provide a package which is already configured to do so. The traffic between the daemon and the cluster must be encrypted to ensure a safe and secure QDevice integration in Proxmox VE.
First, install the corosync-qnetd package on your external server
external# apt install corosync-qnetd
and the corosync-qdevice package on all cluster nodes
pve# apt install corosync-qdevice
After that, ensure that all your nodes on the cluster are online.
You can now easily set up your QDevice by running the following command on one of the Proxmox VE nodes:
pve# pvecm qdevice setup <QDEVICE-IP>
The SSH key from the cluster will be automatically copied to the QDevice.
|
|
Make sure that the SSH configuration on your external server allows root login via password, if you are asked for a password during this step. |
After you enter the password and all the steps are successfully completed, you will see "Done". You can check the status now:
pve# pvecm status
...
Votequorum information
~~~~~~~~~~~~~~~~~~~~~
Expected votes: 3
Highest expected: 3
Total votes: 3
Quorum: 2
Flags: Quorate Qdevice
Membership information
~~~~~~~~~~~~~~~~~~~~~~
Nodeid Votes Qdevice Name
0x00000001 1 A,V,NMW 192.168.22.180 (local)
0x00000002 1 A,V,NMW 192.168.22.181
0x00000000 1 Qdevice
which means the QDevice is set up.
Frequently Asked Questions
Tie Breaking
In case of a tie, where two same-sized cluster partitions cannot see each other but the QDevice, the QDevice chooses randomly one of those partitions and provides a vote to it.
Possible Negative Implications
For clusters with an even node count there are no negative implications when setting up a QDevice. If it fails to work, you are as good as without QDevice at all.
Adding/Deleting Nodes After QDevice Setup
If you want to add a new node or remove an existing one from a cluster with a QDevice setup, you need to remove the QDevice first. After that, you can add or remove nodes normally. Once you have a cluster with an even node count again, you can set up the QDevice again as described above.
Removing the QDevice
If you used the official pvecm tool to add the QDevice, you can remove it trivially by running:
pve# pvecm qdevice remove
Corosync Configuration
The /etc/pve/corosync.conf file plays a central role in a Proxmox VE cluster. It controls the cluster membership and its network. For further information about it, check the corosync.conf man page:
man corosync.confFor node membership you should always use the pvecm tool provided by Proxmox VE. You may have to edit the configuration file manually for other changes. Here are a few best practice tips for doing this.
Edit corosync.conf
Editing the corosync.conf file is not always very straightforward. There are two on each cluster node, one in /etc/pve/corosync.conf and the other in /etc/corosync/corosync.conf. Editing the one in our cluster file system will propagate the changes to the local one, but not vice versa.
The configuration will get updated automatically as soon as the file changes. This means changes which can be integrated in a running corosync will take effect immediately. So you should always make a copy and edit that instead, to avoid triggering some unwanted changes by an in-between safe.
cp /etc/pve/corosync.conf /etc/pve/corosync.conf.new
Then open the config file with your favorite editor, nano and vim.tiny are preinstalled on any Proxmox VE node for example.
|
|
Always increment the config_version number on configuration changes, omitting this can lead to problems. |
After making the necessary changes create another copy of the current working configuration file. This serves as a backup if the new configuration fails to apply or makes problems in other ways.
cp /etc/pve/corosync.conf /etc/pve/corosync.conf.bak
Then move the new configuration file over the old one:
mv /etc/pve/corosync.conf.new /etc/pve/corosync.conf
You may check with the commands
systemctl status corosync journalctl -b -u corosync
If the change could be applied automatically. If not you may have to restart the corosync service via:
systemctl restart corosync
On errors check the troubleshooting section below.
Troubleshooting
Issue: quorum.expected_votes must be configured
When corosync starts to fail and you get the following message in the system log:
[...]
corosync[1647]: [QUORUM] Quorum provider: corosync_votequorum failed to initialize.
corosync[1647]: [SERV ] Service engine 'corosync_quorum' failed to load for reason
'configuration error: nodelist or quorum.expected_votes must be configured!'
[...]
It means that the hostname you set for corosync ringX_addr in the configuration could not be resolved.
Write Configuration When Not Quorate
If you need to change /etc/pve/corosync.conf on an node with no quorum, and you know what you do, use:
pvecm expected 1This sets the expected vote count to 1 and makes the cluster quorate. You can now fix your configuration, or revert it back to the last working backup.
This is not enough if corosync cannot start anymore. Here it is best to edit the local copy of the corosync configuration in /etc/corosync/corosync.conf so that corosync can start again. Ensure that on all nodes this configuration has the same content to avoid split brains. If you are not sure what went wrong it’s best to ask the Proxmox Community to help you.
Corosync Configuration Glossary
- ringX_addr
-
This names the different link addresses for the kronosnet connections between nodes.
Cluster Cold Start
It is obvious that a cluster is not quorate when all nodes are offline. This is a common case after a power failure.
|
|
It is always a good idea to use an uninterruptible power supply (“UPS”, also called “battery backup”) to avoid this state, especially if you want HA. |
On node startup, the pve-guests service is started and waits for quorum. Once quorate, it starts all guests which have the onboot flag set.
When you turn on nodes, or when power comes back after power failure, it is likely that some nodes boots faster than others. Please keep in mind that guest startup is delayed until you reach quorum.
Guest Migration
Migrating virtual guests to other nodes is a useful feature in a cluster. There are settings to control the behavior of such migrations. This can be done via the configuration file datacenter.cfg or for a specific migration via API or command line parameters.
It makes a difference if a Guest is online or offline, or if it has local resources (like a local disk).
For Details about Virtual Machine Migration see the QEMU/KVM Migration Chapter.
For Details about Container Migration see the Container Migration Chapter.
Migration Type
The migration type defines if the migration data should be sent over an encrypted (secure) channel or an unencrypted (insecure) one. Setting the migration type to insecure means that the RAM content of a virtual guest gets also transferred unencrypted, which can lead to information disclosure of critical data from inside the guest (for example passwords or encryption keys).
Therefore, we strongly recommend using the secure channel if you do not have full control over the network and can not guarantee that no one is eavesdropping on it.
|
|
Storage migration does not follow this setting. Currently, it always sends the storage content over a secure channel. |
Encryption requires a lot of computing power, so this setting is often changed to "unsafe" to achieve better performance. The impact on modern systems is lower because they implement AES encryption in hardware. The performance impact is particularly evident in fast networks where you can transfer 10 Gbps or more.
Migration Network
By default, Proxmox VE uses the network in which cluster communication takes place to send the migration traffic. This is not optimal because sensitive cluster traffic can be disrupted and this network may not have the best bandwidth available on the node.
Setting the migration network parameter allows the use of a dedicated network for the entire migration traffic. In addition to the memory, this also affects the storage traffic for offline migrations.
The migration network is set as a network in the CIDR notation. This has the advantage that you do not have to set individual IP addresses for each node. Proxmox VE can determine the real address on the destination node from the network specified in the CIDR form. To enable this, the network must be specified so that each node has one, but only one IP in the respective network.
Example
We assume that we have a three-node setup with three separate networks. One for public communication with the Internet, one for cluster communication and a very fast one, which we want to use as a dedicated network for migration.
A network configuration for such a setup might look as follows:
iface eno1 inet manual
# public network
auto vmbr0
iface vmbr0 inet static
address 192.X.Y.57
netmask 255.255.250.0
gateway 192.X.Y.1
bridge-ports eno1
bridge-stp off
bridge-fd 0
# cluster network
auto eno2
iface eno2 inet static
address 10.1.1.1
netmask 255.255.255.0
# fast network
auto eno3
iface eno3 inet static
address 10.1.2.1
netmask 255.255.255.0
Here, we will use the network 10.1.2.0/24 as a migration network. For a single migration, you can do this using the migration_network parameter of the command line tool:
# qm migrate 106 tre --online --migration_network 10.1.2.0/24
To configure this as the default network for all migrations in the cluster, set the migration property of the /etc/pve/datacenter.cfg file:
# use dedicated migration network migration: secure,network=10.1.2.0/24
|
|
The migration type must always be set when the migration network gets set in /etc/pve/datacenter.cfg. |
Copyright and Disclaimer
Copyright © 2007-2019 Proxmox Server Solutions GmbH
This program is free software: you can redistribute it and/or modify it under the terms of the GNU Affero General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.
This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU Affero General Public License for more details.
You should have received a copy of the GNU Affero General Public License along with this program. If not, see https://www.gnu.org/licenses/